New mobile Phishing Method using fake address bar and scroll locking
Phishing, the attempt to steal important data such as login information, passwords, or credit card numbers from unsuspecting users, is still a major threat on today's Internet. Microsoft's Security Intelligence report saw phishing emails increase by 250% in 2018 alone.
Most web browsers come with certain defenses, usually in form of blacklists and other defensive measures to detect phishing attacks.
One problem with the approach is that it addresses known phishing sites for the most part. The Inception Bar is a new phishing method designed specifically for mobile.
Many mobile web browsers hide the address bar when a user starts to scroll to expand the content of the active webpage. Since space is a premium on mobile, it makes sense to use the address space for that. Doing so removes the strongest identifying indicator for that webpage, and it also makes way for the new phishing method.
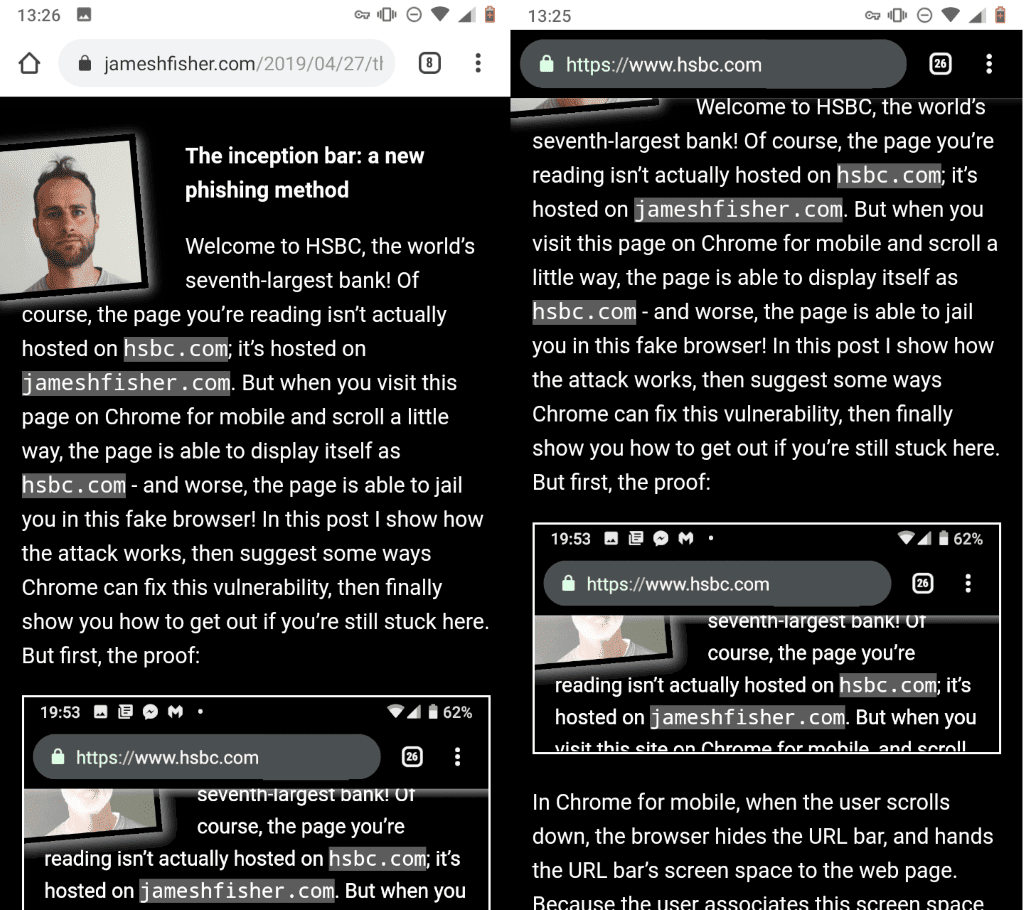
Basically, what the phishing method does is put a fake copy of the address bar at the top of the screen in the fixed location the address bar is found in usually. Browsers would normally display the address bar again when users scroll up but the implementation of a scroll lock on the page prevents that from happening.
The effect is that the fake address bar -- that looks similar to the real one -- is shown to users and that it becomes difficult to exit the page. Even worse, since it is fake, it is possible to make it display any site URL. A dedicated web developer could create a full copy of Chrome's address bar and not just a lookalike.
You can see it in action on James Fisher's website. Note that you will experience this method first hand if you use the mobile version of Chrome to access the site; on desktop, you may watch the animated GIF to see how it works when you connect using mobile devices.
Fisher's method works in Chrome for mobile; he notes that one could check for the user agent to display similar fake address bars for other mobile web browsers.
I accessed the site on Chrome Stable and Chrome Canary for Android. The replacement worked in Canary but it did not in Chrome Stable. Whether that is caused by a setting in the browser or something else is unclear.
You can get out of it by activating any link on the site if you are stuck in mobile Chrome.
Detecting that it is fake
For now, it is easy to detect whether the address bar is real or fake; the tab and menu icons don't do a thing, and it is not possible to edit the URL either.
Things could get more complicated if the phishing method is developed further. Someone could use a form instead that accepts input and make the icons behave more or less like they would.
The tab count that is displayed could still be an indicator, and most users probably know the site they accessed and may notice that the new site displayed is different from it.
Now You: What is your take on this method?
This article was first seen on ComTek's "TekBits" Technology News

- Log in to post comments